Your router’s lights are blinking, but no one is using it. Or you are not getting the internet speed; you paid for. Chances are, your neighbor is using your WiFi without your knowledge. Or let just say, for any other reason you want to see what devices are connected to my network.
Change My MAC - Spoof Wifi MAC 1.7.6 apk free and safe download. Get Change My MAC - Spoof Wifi MAC latest version for Samsung, Huawei, Xiaomi, LG, HTC, Lenovo and all other Android phones, tablets and devices.
Also Read: What to do if You Forget Your WiFi Password
Thankfully, it’s pretty easy to find out who is connected to your WiFi network. All you have to do is install a small app on your device, and it’ll give the list of IP and MAC address of all the devices connected to your network.
So, here are some best apps and methods to find out who is connected to your WiFi network.
1. See who is using your WiFi on Windows
There are several Window’s programs that show you the list of devices connected to your network. The one, I suggest is Wireless Network Watcher by Nirsoft. Like all the other apps from Nirsoft, this one also weight in few KBs and can be executed directly from the .exe file. No installation required.
To get Started, download Wireless Network Watcher from Nirsoft official website (scroll down to the bottom of the page to see the download link). Next, open the zip file and run the .exe in it. If you see a warning from your AntiVirus, ignore it. The app is safe.
The app will display all the connected device, along with their IP and MAC address. It also shows the device’s manufacturer name, like Motorola, Apple, etc, which will help you better identify the devices, since remembering MAC address is not convenient.
You can also set up a sound notification. So when a new device connects to your WiFi, you hear a beep sound. To do that, go to options > beep when a new device is connected.
I also tried other popular alternatives like Advance IP scanner and GlassWire, and both in their free version are similar to Wireless Network Watcher. So don’t bother trying them. And if you are looking for the advanced option, then try Angry IP Scanner or Wireshark, but they need good technical knowledge.
2. See who is using your WiFi on macOS
There is no Mac version of Wireless Network Watcher. And other popular options, which are free in Windows (like SoftPerfect WiFi Guard) becomes paid in Mac ($9). But luckily, there is one app.
Who’s on my WiFi is a free MacOS utility, that does exactly what it says, i.e. it show the list of all devices connected to your WiFi. The app is available on iTunes, and it weighs only 1 MB.
When you open the app, it’ll automatically scan your network and give you the list of all the connected devices. It also gives you a notification when a new device joins your WiFi.
But unlike network watcher in Windows, it’s not that good at fetching the company name of the devices. So, you’ll have to add the names of your devices manually. This way, next time you see a new device, you’ll know it’s not yours.
3. See who is using your WiFi on Android/iOS
There are many apps for Android and iOS, which can tell, who is connected to your WiFi. But the best one is Fing. It’s a free app and is available for both Android and iOS.
Like all the other apps, we have seen so far; Fing also shows you the list of all the connected device along with their IP and MAC address. But what makes it different from rest, is its ability to pinpoint the device name and network card, manufacturer.
For instance, Wireless Network Watcher can only tell the company name. So if you connect an iPad and Macbook, you’ll see Apple written next to it. But Fing on the other hand also manages to extract the device name. So, you can easily tell which devices are yours and which are not. You can also create a free Fing account and keep track of all devices on various WiFi network.
Fing (Android iOS)
Though, one thing missing in Fing is that it doesn’t give you a notification when a new device joins or leave the network. But luckily there one app on Android —WiFi Watch, which can do that. You can enable this notification option from the settings.
4. Router
Using the router to see the list of connected devices has both advantages and disadvantages. The good part is — you don’t have to install any app. But the bad part is, not every user has access to the router and even if they have, it still takes a few extra clicks and the entire process is not quite convenient on mobile.
If you have dynamic DNS setupon your router, you don’t even have to be connected to that network, to see who is connected to your WiFi. This means you monitor your Home network from your office.
To find out who is connected to your WiFi using your router; simply, log in to your router dashboard by typing the router’s IP address in the browser, next type in router’s username and password. If you don’t know what they are, ask the person who has set up the router. Usually, it’s admin and admin or admin or password. You can also use this default router passwords database.
Next, you’ll see a router ‘web interface’. Now, since all the router are made by different manufacturers, your Router’s interface may look different from mine. But the core is always the same. So, look for options that say,- DHCP Client list, Attached Devices, Wireless, Connected Devices, etc.
Usually, it’s under the Wireless settings. And there, you’ll see the list of all the devices along with their IP and MAC address.
If you are not sure where to find them, do a quick Google search of your router manual and use CMD + F or CTRL +F, to find what you need. I do this all the time.
What to do if Someone is Stealing Your WiFi?
Although we are taught – sharing is caring, it doesn’t hold true when security is involved. Anyone connected to your local network will have access to files shared on the network and can also see your browsing activity. Not to forget, they are also leeching on your precious bandwidth.
So here are a couple of things you can do if someone using your WiFi without your permission.
#1 Change the WiFi password or enable MAC filtering. Both options are present in every router.
#2 In some routers you can decrease the WiFi strength so that the signal won’t go outside your home parameter.
#3 Kick unauthorized people off your network. You can do that by using WiFiKill the app on Android [Root] or another way of doing that, is replicating their IP Address, or by using software to disconnect people from your current WiFi network.
Related: 5 Ways To Kick People Off Your WiFi Network
#4 If you are good with technical stuff, you can also find their location (accurate up to a few meters) using a network analyzer app and then confront them personally. Though, you might need a bodyguard or two this time. You never know, who you find.
However, this is not a full proof method, because it’s pretty easy to spoof Mac address and if some hacker is stealing your Wi-Fi, they probably have spoof their Mac address. Therefore, I suggest you check their Mac address to see if it change all time or stay consistent. If it changes then chances, are they are using the software. At this time, it’s better to increase your router security by using a complex WiFi password with WPA2 encryption.
Related: 10 Steps to Secure Your Wi-Fi Network From Hackers
Wrapping Up
So, these were some simple ways to find out who is connected to your WiFi network. If you suspect, someone is stealing your internet, the best time to run the scan will be when you are getting low internet speed or facing any other network problems.
Also, usually, it’s hard to identify the devices, by looking at their IP and MAC address. One way to fix this is, simply turn off the Wi-Fi on each of your devices one by one to figure out which one is what. And for the future, I suggest you write down the last two digits of their mac address so that you know which one is what.
Updated: January 4, 2020 Home » Computer and Internet Security » WiFi Security
Is someone stealing your wifi? How to find out if your neighbor hacked your wifi password? If you internet is slow for some unknown reason and your bandwidth was drained faster than normal, it is time to check and see if someone, especially your neighbor is stealing your wifi.
Alternative 2020 Article ➤ 3 Methods To Recover And Retrieve WiFi Password- Reveal WEP WPA Security Key
How to find out if your neighbor is stealing your internet? Below are 5 simple software that allows you to ping which devices is connected to your router. By using these tools, you are able to know how many devices are connected to your router and if there are any unwanted devices that are not authorized to access it. Some advice:
- Always change the default router’s password.
- Always change your router’s WiFi password on a yearly basis.
- Use WPA2, WEP can be crack within minutes.
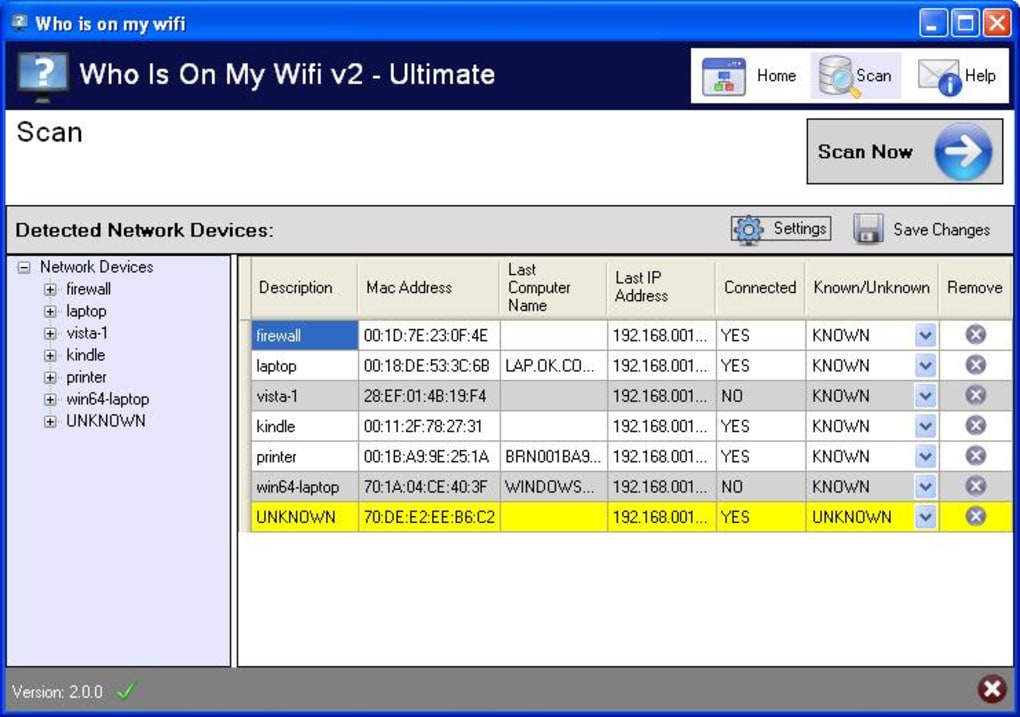
↓ 01 – Who Is On My WiFi Windows and macOS
Who’s On My Wifi solutions are built to be as easy as possible to detect unknown devices on your home or business network. We focus on building unique solutions for homes and small businesses instead of just stripping down complicated enterprise products. And we work hard everyday to make them easier to use over time.
- Shows all devices on a network overtime.
- Connects with Optional Analytics Subscription.
- Easy to Install on Windows computers.
- Fully Compatible with Analytics Subscription
- Agent per Subnet based detection
- DHCP Server per Scope based detection
- Includes Privacy and Shared Key Features
↓ 02 – SoftPerfect WiFi Guard Free for Windows, $10 for macOS
SoftPerfect WiFi Guard is an essential tool for everyone running a small wireless network and striving to keep it secure. Generally, modern Wi-Fi networks are well protected, but there are a number of weaknesses that can compromise your Wi-Fi password; this includes vulnerabilities in encryption and brute force attacks. As a result, someone can gain unauthorised access to your Internet connection and LAN and exploit them while staying unnoticed.
Here comes our little application: it will alert you if your network is used without your knowledge. WiFi Guard is a specialised network scanner that runs through your network at set intervals and reports immediately if it has found any new, unknown or unrecognised connected devices that could possibly belong to an intruder.
Key features
- Pings computers and other network devices and displays those alive.
- Detects firewalled computers that do not respond to ping.
- Scans your network at a specified interval.
- Immediately alerts you if an unknown device is found.
↓ 03 – Advanced IP Scanner Free Windows
Free and fast network scanner allowing you to quickly retrieve information about network devices and get access to their various resources such as shared folders, HTTP, HTTPS, FTP, RDP and Radmin. The program does not require installation and has a simple and user-friendly interface. Advanced IP Scanner is widely used by system administrators and home users for network management and monitoring.
Reliable and free network scanner to analyse LAN. The program shows all network devices, gives you access to shared folders, provides remote control of computers (via RDP and Radmin), and can even remotely switch computers off. It is easy to use and runs as a portable edition. It should be the first choice for every network admin.
↓ 04 – Wireless Network Watcher Free Windows
Wireless Network Watcher is a small utility that scans your wireless network and displays the list of all computers and devices that are currently connected to your network. For every computer or device that is connected to your network, the following information is displayed: IP address, MAC address, the company that manufactured the network card, and optionally the computer name.
↓ 05 – Angry IP Scanner Free Windows, macOS and Linux
Angry IP Scanner (or simply ipscan) is an open-source and cross-platform network scanner designed to be fast and simple to use. It scans IP addresses and ports as well as has many other features. It is widely used by network administrators and just curious users around the world, including large and small enterprises, banks, and government agencies. It runs on Linux, Windows, and Mac OS X, possibly supporting other platforms as well.
- Scans local networks as well as Internet
- IP Range, Random or file in any format
- Exports results into many formats
- Extensible with many data fetchers
- Provides command-line interface
WEP vs. WPA vs. WPA2 Comparison
How do Wifi wireless get hacked? With the right software such as Air Crack or Backtrack, one can easily break any WEP encryption keys. What AirCrack does is it gathers all the data transmit between your router and your devices, compile it and then compute all the possible combination. With today’s processing power and the weakness in WEP, it takes less than 10 minutes to reveal your WEP security key on a busy network.
Deauthorizing Wireless Clients with Aircrack-ng, the four-way-handshake and WEP vs WPA cracking
WPA has its own weakness to, but it is harder to crack. WPA2 is highly recommended for SME or enterprise; remember than anything man made can be un-made. WPA2 is crackable too, but it will require too much effort and time. It is easier for the hacker to look for someone using WEP instead of wasting time breaking the WPA2 security code. Below is a simple side by side comparison between WEP, WPA and WPA2.
WEP | WPA | WPA2 | |
|---|---|---|---|
| Name | Wired Equivalent Privacy | Wifi Protected Access | Wifi Protected Access 2 |
| Combo | 24 bit initialization keys 16.7 million combination | 48 bit initialization keys 500 trillion combinations | 48 bit initialization keys 500 trillion combinations Advanced Encryption Standard |
| Encryption | 64 bits 128 bits | 64 bits 128 bits | 64 bits 128 bits |
| Keys | Static encryption keys | Unique encryption key | Unique encryption key |
| Speed | Not much processing power | Somewhat processing power | Requires greater processing power |
| Master Key | Master keys are used directly | Master keys are never directly used | Master keys are never directly used |
